مستند تعريفي
العنوان
العميل
التاريخ
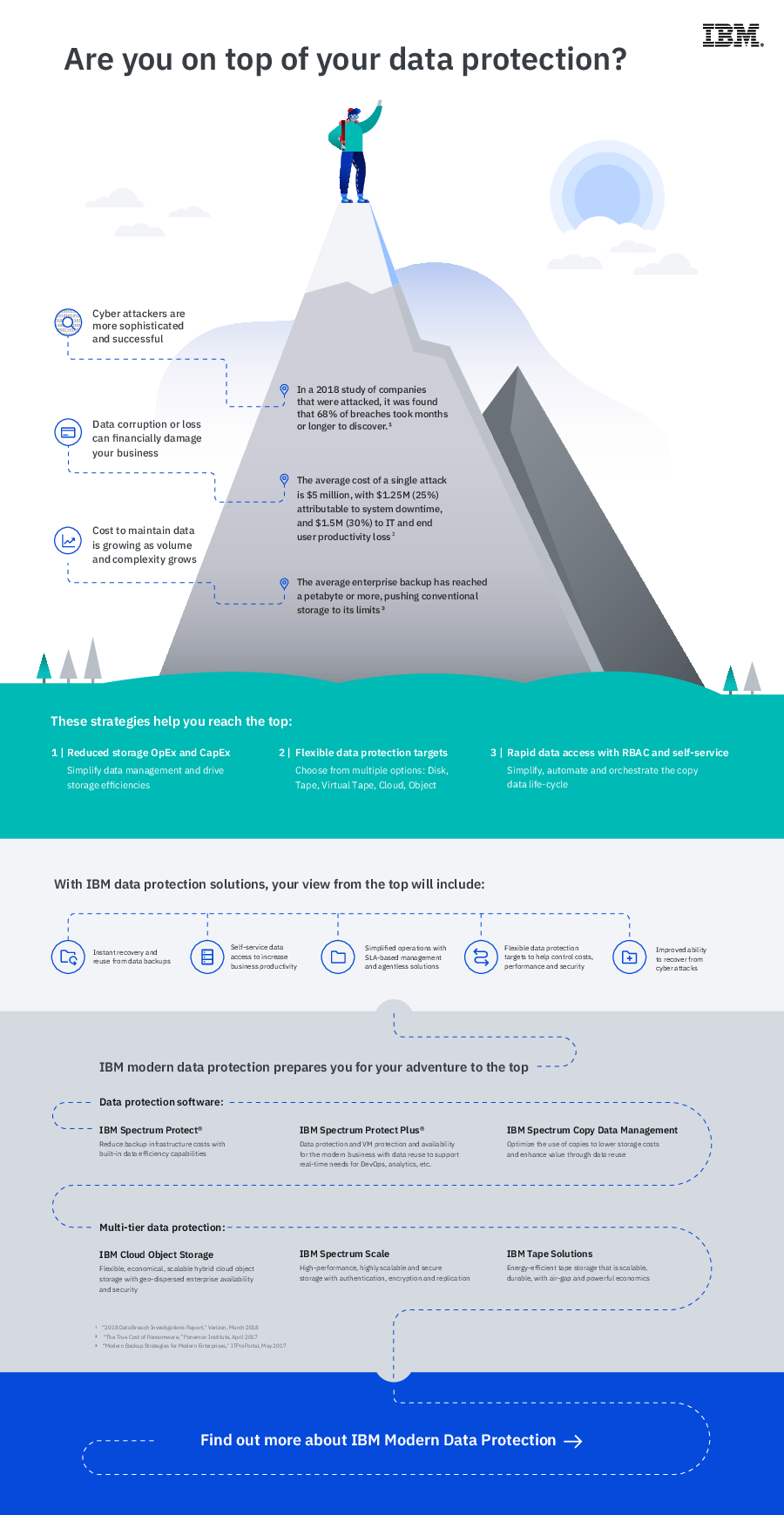
Experience the simplicity of data protection and availability, for free The cost and care that need...
IBM
2019-07-17
5 Backup Necessities for the Modern Enterprise Backup has changed significantly over the past decad...
Commvault Systems Ltd
2019-07-11
Government body safeguards infrastructure, applications, and devices in the field with single backup a...
Commvault Systems Ltd
2019-07-11
Construction firm reduces costs, complexity and risk by protecting information in the cloud and at rem...
Commvault Systems Ltd
2019-07-11
Orchid Pharma significantly cuts hardware costs with Commvault Pharmaceutical company reduces disk ...
Commvault Systems Ltd
2019-07-11
Quickly protect, manage and recover enterprise data Enterprise organizations deploy a wide range of...
Commvault Systems Ltd
2019-07-11
IT departments can no longer keep up with the massive complexity of the underlying worlds they manage....
Commvault Systems Ltd
2019-07-11
Why Backup Breaks and How to Fix it For most organizations backup, the process of regularly and con...
Commvault Systems Ltd
2019-07-11
5 practices to ensure that you can backup everywhere and recover to anywhere Enterprises are cobbli...
Commvault Systems Ltd
2019-07-11