Bijela knjiga
Naslov
Klijent
Datum
The growth and evolution of ransomware is one of the most destructive trends of the last decade. This ...
Veeam Pty. Ltd
2022-09-23
Business data is growing across multiple facets of the modern enterprise, and new types of information...
Veeam Pty. Ltd
2022-09-23
The pace for change in IT continues to rise, but how exactly are companies adapting for Modern Data Pr...
Veeam Pty. Ltd
2022-09-23
As consumers and customers, we are accustomed to easy, intuitive and superfast transactions driven by ...
Veeam Pty. Ltd
2022-09-23
Are you and your team considering all the facets of a new data management strategy? This 451 Resear...
Veeam Pty. Ltd
2022-09-23
Citrix Virtual Apps and Desktops enables you to centrally manage virtual apps and desktops, giving use...
Citrix Systems GmbH
2022-09-22
Recent years have made it clear that employees need anytime, anywhere access to the information and ap...
Citrix Systems GmbH
2022-09-22
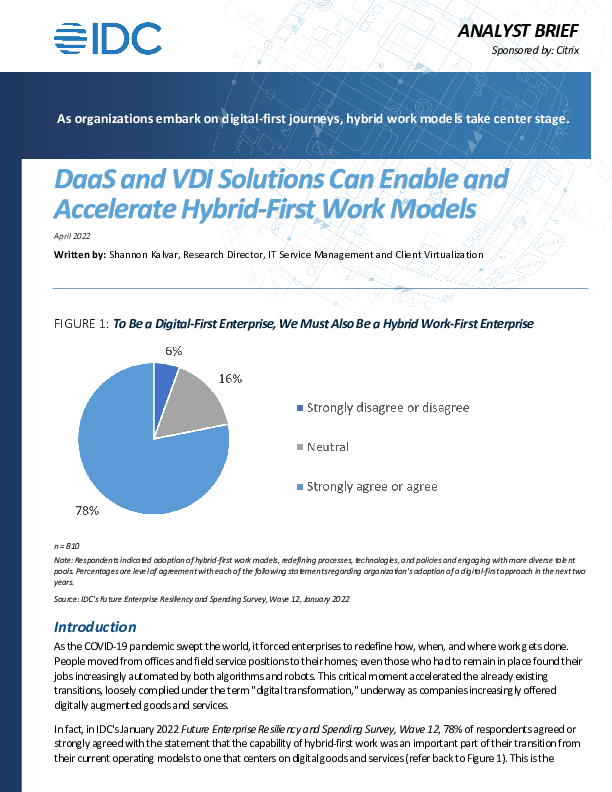
As the COVID-19 pandemic swept the world, it forced enterprises to redefine how, when, and where work ...
Citrix Systems GmbH
2022-09-22
The pandemic and its accompanying disruptions changed forever how enterprises think about, acquire, an...
Citrix Systems GmbH
2022-09-22