
Klient: Fortinet UK Limited
Format: Checklista
Storlek: 67,7 KB
Språk: Engelska
Datum: 03.11.2021
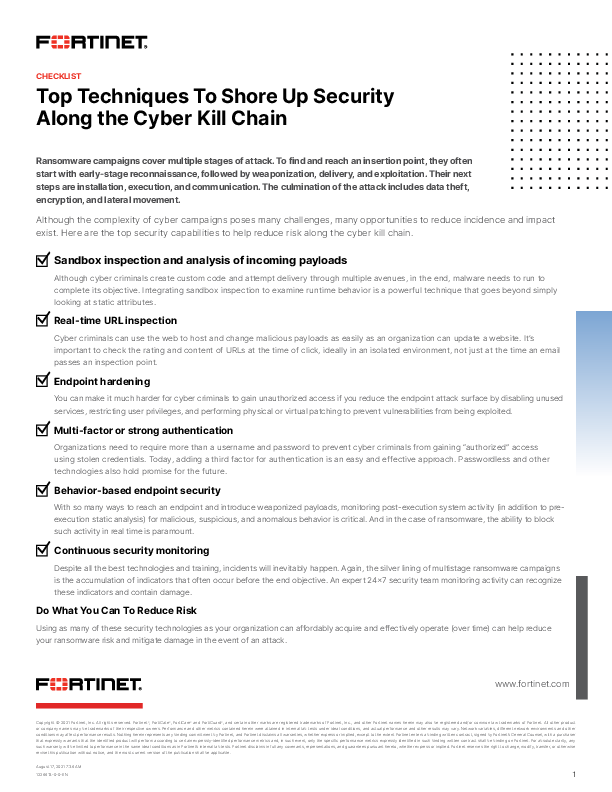
Top Techniques To Shore Up Security Along the Cyber Kill Chain
Ransomware campaigns cover multiple stages of attack. To find and reach an insertion point, they often start with early-stage reconnaissance, followed by weaponization, delivery, and exploitation. Their next steps are installation, execution, and communication. The culmination of the attack includes data theft, encryption, and lateral movement.
Although the complexity of cyber campaigns poses many challenges, many opportunities to reduce incidence and impact exist.